Once you have your content selected, whether it’s text or an image, all you have to do is press two keys.
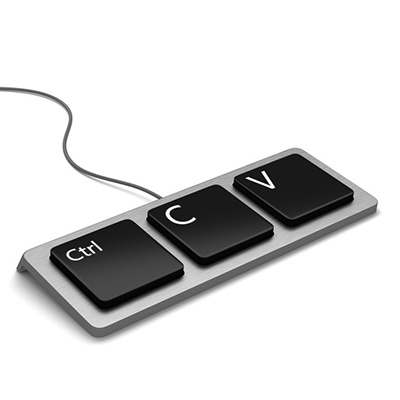
To cut a word or phrase from one place in your content, press Ctrl + X. To copy this content instead, keeping the original and duplicating it elsewhere, press Ctrl + C. Pasting your content is just as simple – with the place you want the content added selected, press Ctrl + V. This will insert your content where you want.
If you happen to be copy-pasting from a website to another document, it may not be a bad idea to paste it without bringing any formatting from the website over. Otherwise, it is apt to look funny on your documents. Pasting without formatting is almost as simple as regular pasting, you just add another keystroke in the middle: Ctrl + Shift + V.
Of course, any of the tasks can be accomplished with the mouse alone. Right clicking on a word, an image, or a group of selected text will bring up a menu that includes all of the above options. However, your cursor is generally more accurate than the mouse, so you may have to undo your efforts (Ctrl + Z) a few times before it’s right.
Real World Example:
Let’s say you want to send a webpage link to someone in an email or instant message. In your web browser, click the address bar (that’s the part with the ‘http://… “). That will highlight the URL. Hold down Ctrl and press C. Then go into your email or instant messenger, click where you want to paste the URL, and hold down Ctrl and press V.
Whichever you use, it’s bound to be more time-efficient than rewriting anything that needs to go in a different spot. Make sure you subscribe to our blog, so you can be alerted whenever we upload more content!